What is Managed Attribution?
Managed attribution is the holistic and deliberate act of curating digital signatures and forensic artifacts to project a desired image online.
This article was adapted from a blog post originally published on Philip’s personal website on May 15, 2025. It has been updated and edited for clarity.
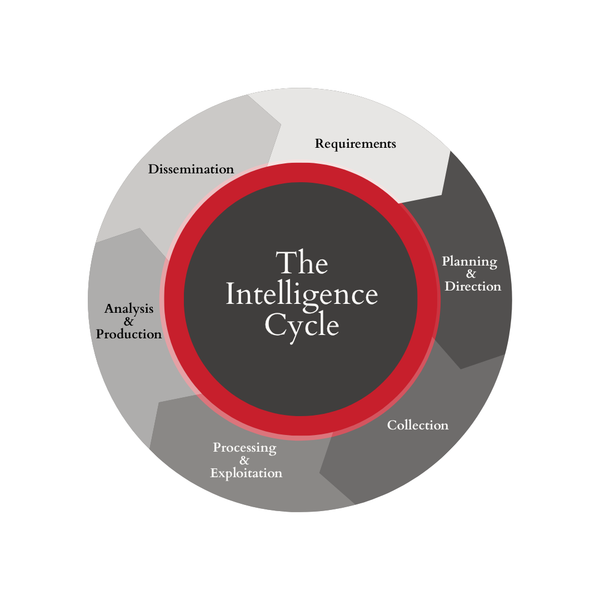
Information becomes intelligence when it is relevant, timely, and useful. The art of collecting intelligence is a continuous evolution, but one constant remains—counterintelligence. Whether your goal is to identify and counter terrorist threats, defend against hackers, or gather information online as a journalist or academic researcher, it's crucial to understand the variety of ways you may expose yourself and your research while online.
A valuable source of information can quickly devolve into a poisoned well of deception when an adversary becomes aware of your interest. In a worst-case scenario, this may even manifest as real-world threats against a researcher’s personal safety. How do we carry on safely, and ensure our collection stays relevant, timely, and useful, all while avoiding the many pitfalls that exist online?
First, acknowledge one universal truth: everyone makes mistakes. An increasing number of security vendors offer managed attribution platforms, but there is intangible value in the thoughtful development of a managed attribution strategy. There are countless examples of organizations spending untold sums on sophisticated managed attribution platforms, only to have a well-intentioned employee, in the midst of a professional crisis, log in to a research account from a personal device or network the very next day.
Before proceeding, a definition of terms is in order.
Attribution is the process of assigning an observed behavior or activity to a group or individual based on analysis of digital signatures and forensic artifacts. Over the last ten years, the discussion surrounding attribution has steadily evolved. In the early days, organizations aimed for the lofty goal of non-attributable online activity; however, this goal was neither practical nor realistic for most.
Non-attribution requires that an activity or event cannot be attributed to any entity because no digital signatures, forensic artifacts, or other evidence of the activity persists—think self-destructing messages. This goal was likely a holdover from the Cold War school of clandestine activity when intelligence services and special operations teams sought to infiltrate an adversary's physical borders, carry out some activity, and escape without detection. While this type of activity may still persist in the physical world to some degree, it is virtually impossible in the digital world where every click, keystroke, and scroll is logged and monetized.
When it becomes impossible or impractical to carry out clandestine activity without detection, some turn to misattribution, or the act of causing an activity or event to be attributed to a specific group or individual other than that which carried it out. In practice, this most commonly manifests as deception. Online, it could be a persona masquerading as a member of a specific organization, or the use of compromised infrastructure to obfuscate the origin of malicious network traffic.
Misattribution may exist as a component of a managed attribution strategy, but it's often not practical as a holistic approach to online research and operations due to the intense level of effort required for success, as well as potential legal and ethical concerns surrounding both the misdirection of investigative efforts onto another party and the potential to draw investigative interest to benign activity.
Introducing, Managed Attribution
Managed attribution is the holistic and deliberate act of curating digital signatures and forensic artifacts to project a desired image online. Managed attribution leverages a broad range of techniques and resources to diversify behavioral indicators, obfuscate digital signatures, inject noise or randomness where appropriate, and minimize or craft forensic artifacts. This approach addresses numerous goals and outcomes through a variety of tailored solutions based on individual circumstances. The key to a successful managed attribution strategy lies not in software or hardware, but in flexibility, adaptability, and a positive user experience. If the system isn't easy to use, it will fail.
The goal of curating your digital footprint online should exist whether you're a leading threat intelligence provider or an independent journalist. While managed attribution platforms can be expensive, managed attribution doesn't have to be. It is possible for an individual of modest technical ability to configure a reasonably secure, low-cost approach to managing their digital footprint online using freely available software and a commercial VPN subscription. The challenge lies in the path to execution.
When designing a managed attribution strategy, it is important to set ground rules and consider the various use cases it should address. In this series, we’ll cover suggested guardrails and a potential use cases:
- Account Management
- Data Processing and Analysis
- Passive Browsing
- Subscription-based Accounts
- Fictitious Personas
- Online Operations
- Scanning and Automation
In the coming weeks, we’ll break down each of these use cases, detailing the specific guardrails and actionable strategies required to operate safely in these environments.
Are you interested in learning more about managed attribution? Our paid subscribers get early access to AMAs, webinars, and premium content.