The Low Bar: How Subpoenas Compel User Data
This analysis examines federal grand jury subpoenas, data collected by companies, and the resulting privacy implications

Kayla is a former FBI special agent who handled national security cyber, criminal cyber, and counterterrorism cases. She served on the Crisis Negotiation Team and Evidence Response Team.
Picture this: You are in the process of buying a home. You receive a call from your realtor that it is time to wire the down payment, but you assure your realtor that you sent the down payment days ago after receiving the wiring instructions from the realtor. The realtor insists that wiring instructions were never sent.
What is happening?
The realtor’s email account was compromised and used by a cybercriminal to send you fraudulent wiring instructions. The down payment you sent is long gone and you are unable to move forward with purchasing your home.
This is known as a business email compromise (BEC) that targets real estate. Thousands of people in the United States are victims of these scams every year. BECs devastate families and their sense of security.
In 2025, the FBI’s Internet Crime Complaint Center (IC3) received 1,008,597 complaints and reported a staggering loss of $20.877 billion. BECs accounted for 24,768 complaints and over $3 billion in loss.
Fortunately for some victims, IC3 has been able to assist in freezing funds through the Financial Fraud Kill Chain (FFKC). For others, they absorb the loss.
The Investigation
Cybercriminals mask their identities and locations with obfuscation techniques, such as using VPNs and creating fake online accounts. Cybercriminals leave a long digital footprint.
Investigators can follow the digital trail by serving federal grand jury subpoenas to companies hosting accounts or digital infrastructure used by cybercriminals.
What is a federal grand jury subpoena?
It is a legal, written order that requires an individual or entity to provide tangible evidence, subpoena duces tecum, or testimony, subpoena ad testificandum, in a federal investigation.
Who approves a federal grand jury subpoena?
A United States Attorney’s Office. For example, to serve a subpoena to Google for records related to a Gmail account, an agent sends a request to the Assistant United States Attorney (AUSA) assigned to the case. The AUSA’s office approves the request, prepares the subpoena for service, and then returns it to an agent who serves it to Google.
What is the legal requirement to obtain a federal grand jury subpoena?
The account must be relevant to the investigation to pass the legal threshold for approval. This is an extremely low bar, which is why subpoenas are issued more frequently than search warrants. A search warrant requires probable cause—articulated through an affidavit—and must be approved by a judge.
Cybercrime investigators frequently direct their subpoenas to Electronic Communication Service (ECS) and Remote Computing Service (RCS) providers, such as social media companies or email providers. The Electronic Communications Privacy Act and the Stored Communications Act (SCA) regulate how the government can legally access information from providers.
In the FBI, policy requires investigators to weigh investigative steps with individual privacy afforded by the Constitution. To do this, the FBI implements a concept called “the least intrusive means”.
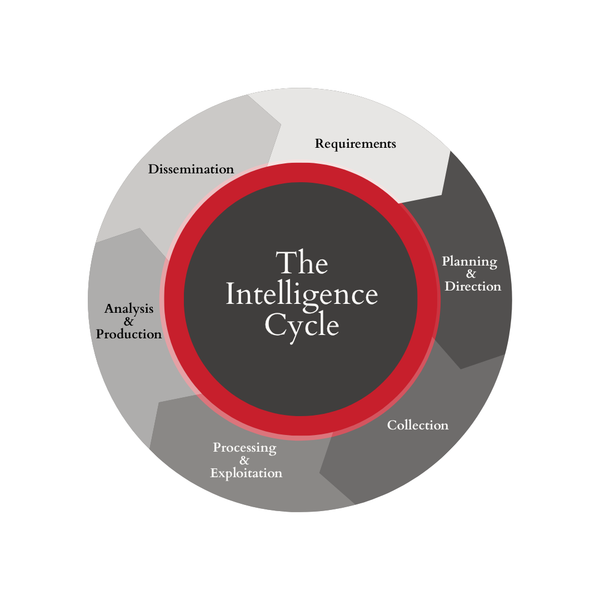
Subpoenas are low on the intrusive scale due to their minimal intrusion into an individual’s privacy; whereas search warrants are high on the intrusive scale due to their greater degree of intrusion into an individual’s privacy. Steps that are less intrusive are generally used early in an investigation. If supporting evidence is revealed, then more intrusive steps may be taken.
As the level of intrusiveness increases, so does the legal threshold required for implementation.
Note: This is a simplistic explanation, and not all investigations follow a linear pattern, particularly if there is a threat of death or serious physical injury.
What information does the subpoena compel companies to produce?
- Basic subscriber information:
- name;
- address;
- local and long distance telephone connection records, or records of session times and durations;
- length of service (including start date) and types of service utilized;
- telephone or instrument number or other subscriber number or identity, including any temporarily assigned network address; and
- means and source of payment for such service (including any credit card or bank account number)
Depending on what a provider stores, the subpoena return can reveal quite a bit about a user. Multiple accounts associated with a cybercriminal can provide an outline of the cyber criminal’s life without the content of emails, direct messages, or other communications.
For example, a subpoena return may include a user’s IP address every time the user logs into and out of the account. A Whois lookup can be conducted on an IP address and, if not masked, may disclose a person’s general location, internet service provider, and/or phone service provider. Additional subpoenas can be served to those providers, supplying additional information.
While a subpoena’s intrusion into an individual’s privacy is minimal compared to a search warrant, subscriber data collected by companies has grown and reveals more about an individual than in past decades.
“What does this have to do with me?”
In 2026, there have been stories involving privacy and subpoenas impacting real, everyday people – like you.
Don’t miss Part 2, where I will share further insights.
In a democratic society, people have the right to know how federal agencies apply the law to investigations and how this impacts people’s privacy. That’s why we’re bringing our expertise to the public square.
Want to become a supporter of democratizing intelligence? Consider subscribing to our Obsidian tier.
Want to learn more about how you can protect your privacy online? Check out our training or services page for more information.